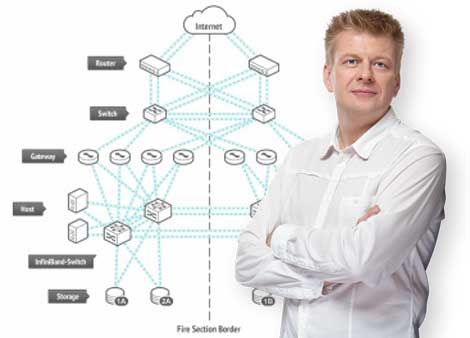
Achieving optimal performance of ICT infrastructure has never been an easy task. However, this goal has become even more elusive, given changes to the architecture of underlying modern IT infrastructures. Today, applications are typically housed in a combination of organization-owned data centers and hosting providers, networks are a combination of public and private networks, and end-user devices may include anything from desktops and laptops to mobile devices and tablets. ICT users themselves have changed their computing habits and want immediate network access, irrespective of where they’re located or to what networks they’re connecting. Collectively, these factors have had a large impact on users’ quality of experience when connecting to business applications over the network. This is a direct result of the different traffic patterns and traffic flows that these trends and behaviors are introducing to the network. Many of today’s networks weren’t designed to carry changing traffic patterns, and in addition, many protocols widely used today aren’t designed to function over a WAN.
Yamamah’s Network Optimization Assessment
Yamamah’s Network Optimization Assessment (NOA) is a network assessment service that helps organizations
Navigate the difficult waters of network performance. It delivers a performance baseline on the network and provides an analysis of the various traffic types, patterns and flows. The information delivered by the assessment allows organizations to understand their networks more intimately and highlight areas and applications that need performance improvement.
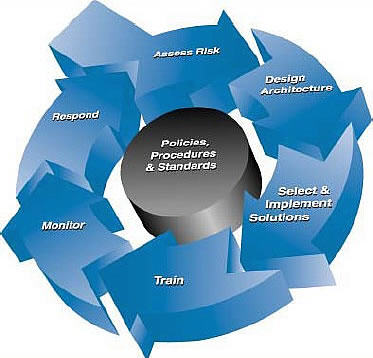
Our approach
The Network Optimization Assessment was designed to provide quality network performance statistics, along with actionable recommendations, quickly. The assessment is delivered in three phases, namely:
Discover phase
The discovery phase is the first step in the assessment and represents the information gathering phase. We use three mechanisms to collect data:
Network statistics collection.
We deploy an appliance onto the network that collects performance data for a defined period. This is the core part of the discovery phase, and the information gathered forms the basis of the report that’s generated from the assessment.
Business interview.
The business interview is used to gather information on the business applications in use, as well as the organization’s strategy related to consolidation, virtualization, mobility, new business applications and a number of other areas that affect network performance.
Technical interview.
The technical interview is used to gather information related to the size and complexity of the network, as well as the views related to performance measurement and support philosophy. Specific network issues are highlighted, where applicable.
Construct phase
During the construct phase, Yamamah analyses the data collected during the discovery phase and begins preparing its report.
Recommend phase
Using the information gathered in the discover and construct phases, Yamamah utilizes its expertise in protocols, networking, data centers and applications to make recommendations on how network performance can be improved. We compile a detailed report, containing information on the traffic patterns that exist on the network, along with recommendations for performance improvement. Yamamah’s Network Optimization Assessment was developed based on our expert knowledge of networking and protocols, and assists organizations with:
Performance statistics.
The service provides a detailed analysis of the traffic statistics collected during the assessment period, including application discovery, network efficiency and overall utilization.
Identifying application and performance problems.
The report will highlight poorly performing applications or points on the network, to enable faster performance problem diagnosis.
Identifying problems before they occur.
Certain traffic patterns may be clearly problematic − these will be analyzed and highlighted during the service.
More informed network planning.
Without detailed knowledge of your network usage and traffic patterns, it’s unlikely that you’ll be in a position to make good planning decisions.
Improved network security posture.
It’s possible that your network bandwidth is being consumed by unauthorized, unwanted and malicious traffic. Once this has been identified, it’s easier to block this type of traffic.
Better selection of performance technologies.
Once traffic patterns are understood, it becomes clear what needs to be done to improve the performance of the network. Choosing the most appropriate technology to address any performance problems becomes easier when using this information.